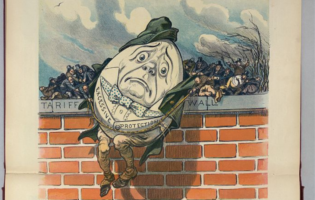
In a World of Cyber Threats, Isolationism Will Never Win

Sarah Lohmann
Dr. Sarah Lohmann is Non-Resident Fellow with the American Institute for Contemporary German Studies at Johns Hopkins University. Dr. Lohmann is an Acting Assistant Professor in the Henry M. Jackson School for International Studies and a Visiting Professor at the U.S. Army War College. Her current teaching and research focus is on cyber and energy security and NATO policy, and she is currently a co-lead for a NATO project on “Energy Security in an Era of Hybrid Warfare”. She joins the Jackson School from UW’s Communications Leadership faculty, where she teaches on emerging technology, big data and disinformation. Previously, she served as the Senior Cyber Fellow with the American Institute for Contemporary German Studies at Johns Hopkins University, where she managed projects which aimed to increase agreement between Germany and the United States on improving cybersecurity and creating cybernorms.
Starting in 2010, Dr. Lohmann served as a university instructor at the Universität der Bundeswehr in Munich, where she taught cybersecurity policy, international human rights, and political science. She achieved her doctorate in political science there in 2013, when she became a senior researcher working for the political science department.
Prior to her tenure at the Universität der Bundeswehr, Dr. Lohmann was a press spokeswoman for the U.S. Department of State for human rights as well as for the Bureau of Near Eastern Affairs (MEPI). Before her government service, she was a journalist and Fulbright scholar. She has been published in multiple books, including a handbook on digital transformation, Redesigning Organizations: Concepts for the Connected Society (Springer, 2020), and has written over a thousand articles in international press outlets.
President Trump has said cybersecurity is a priority for his administration. It is also one of the fastest growing spending priorities for the U.S. government this fiscal year. Across the Atlantic, Germany is preparing to launch new cyber defense capabilities of its own in the wake of massive cyber breaches of government and public sector systems. This piece outlines what threats exist, and what reforms are being and should be undertaken by both countries to fix them.
As the United States and Germany face challenges stemming from common actors to their electoral process through cybersecurity hacks and online disinformation campaigns, they risk turning inward to fix security problems that trespass nation-state boundaries. It would be ill-advised to stay on this course.
The head of Germany’s domestic intelligence agency has warned that the Kremlin is trying to “influence public opinion and decision-making processes” due to Germany’s upcoming parliamentary election in September.[1] Chancellor Merkel has warned that such Russian Internet-based propaganda could interfere with the campaign, which will also determine who will become the next chancellor. At the same time, U.S. intelligence agencies released a report last month that detailed Russia’s influence on the U.S. election through cyber hacks on the Democratic National Committee and to individual Republican accounts.[2] While attacks on these two democratic allies could be viewed in isolation, the consequences of those actions cannot be. The global impact of cybersecurity casualties to U.S. and German security, the economy, and the global balance of power is too great for each nation to respond alone.
In addition to ensuring that both nations strengthen their domestic cybersecurity capacities, there should be:
1.) Transatlantic cooperation through information sharing to prevent new threats and to identify sourcing of those that are ongoing;
2.) An increase in private sector cyber and tech firms’ involvement on the front end of policy discussions on cybersecurity to ensure effective risk management and more functional early warning systems; and
3.) Agreement on cybersecurity norms and how to penalize actors who intentionally cause harm.[3]
The Threat
Globally, the United States and Germany are the two countries whose economies suffer the greatest losses from cyberattacks. Attacks on cybersecurity cost the United States economy $15.4 billion per year, and the German economy an average of $13 billion per year.[4] This continues to increase yearly, with the damage to the global economy due to cyber attacks estimated to be $2.1 trillion by 2019. This means not only the loss of hundreds of thousands of jobs in each country, but also challenges to the functions of national security.
Since 2015 alone, there have been cyber attacks on the Pentagon, the Bundeswehr, the Bundestag, major U.S. and German political parties, power networks, the telecommunications industry, television stations, hospitals, and military armaments. Hacking into the systems of the U.S. defense industry has meant theft of data on the F-35 Joint Strike Fighter, the F-22 Raptor fighter jet, and the MV-22 Osprey, undermining U.S. military advantage.[5] Over 47 million hacker attacks were recorded on the Bundeswehr in 2016, with 9 million rated as forming a high security threat.[6] While that’s down from the 70 million hacker attacks on the Bundeswehr in 2015, it’s an increase in high security threats from 8.5 million that year.[7]
In the United States, Russian-sourced hackings and troll farm campaigns used to promote Donald Trump over Hillary Clinton were reported to interfere with the democratic process. In Germany in 2016, similar Russian-sourced campaigns used to spread disinformation about refugees and dissatisfaction with Angela Merkel, and hacking the Bundestag and her Christian Democratic Party, should be cause enough for both countries to have concern about common threats to their national security and the new balance of power that can proceed from countries turning toward isolationism and away from cooperation.
The Solution
What can Germany and the United States do to deal with these threats? Both countries are naturally looking inward first to provide their defense departments with increased spending to handle the problem. Efficient management of those funds, and streamlined communication across the other government agencies likewise being granted additional funding for fighting cyber threats, will be vital. In the United States, a lack of coordination between cyber centers across many different agencies has slowed information-sharing and threat prevention. In Germany, spending increases and coordination are finally happening, but too little, too late. And for the last three years, both countries have been slow to share what they know about common cyber threats with each other, or to cooperate closely on solutions, as they have in the past.
Germany’s Status Quo and Room to Grow
The Bundeswehr divides its cybersecurity capacities into three areas: A Computer Emergency Response Team (CERT) for the Bundeswehr’s networks and systems, a Computer Network Operations (CNO) team that conducts reconnaissance and intelligence, and a new cyber and information domain command (CIR) in the Ministry of Defense with 300 officers and 13,500 soldiers and civilians (taken mostly from current personnel) to be operational between April and July this year.[8]
It has also created a new cyber center on the Munich campus of the Universität der Bundeswehr to be ready by 2018, with 11 professors and 267 researchers. The German defense ministry earmarked $4.1 million to be spent to recruit an additional 1500 IT professionals for its new cybersecurity unit in the Bundeswehr this last year.[9] While the German interior ministry’s cybersecurity strategy calls on the private and public sectors to work together on raising standards and for Germany to actively place itself in cooperation with European and global cybersecurity efforts, German readiness and forward resilience to ensure future threats are thwarted will take years.[10]
Actors and Action on Cybersecurity in a New U.S. Administration
“There is growing demand for a larger federal cybersecurity budget. This was demonstrated by the 35 percent increased budget request” from last fiscal year to this one, Congressman Brad Sherman’s (D-CA) legislative director Lauren Wolman said in an interview in January 2017. In fiscal year 2017, President Obama asked for $19 billion to be spent on cybersecurity across the U.S. government, an increase of $5 billion from 2016.[11] In the Department of Defense’s (DoD) 2017 budget alone, $6.7 billion was allotted for cyber defense and offense capabilities, an increase of $900 million to the previous year.[12]
What to do with that funding, especially since there are cybersecurity units set up across so many government agencies? The Pentagon’s use of funding for cyber will have oversight from the new subcommittee on cybersecurity created by the Senate Armed Services Committee (SASC) last month. Senator Mike Rounds (R-SC), who is chairing the subcommittee, will be conducting investigations into the DoD’s Cyber Command, which now has the status of a unified combatant command under the newly passed 2017 National Defense Authorization Act. He will also be helping the Pentagon form a prevention and response strategy for cybersecurity, and is focused on attacks harming U.S. critical infrastructure, such as electrical grids, transportation, and water supplies.[13] The House Foreign Relations Committee is employing a two-fold strategy to deal with cyber threats in the new administration, according to Congressional staff. To deal with cyber hacks and data breaches, the Committee will be focused on ensuring the Department of State modernizes its digital platforms and information technology systems to deploy defensive capability that prevents future successful cyber attacks. Here, the Committee is looking at next threats coming from Iran and North Korea.
“Russia is now past tense,” House Congressional staffers said. “We are looking at newer, greater threats. China has more personnel, financial, and infrastructure resources than Russia. They have ten times the number of troll farms,” they said, referring to social media users hired to make inflammatory or misleading comments to influence public opinion.
To respond to disinformation campaigns, the Committee’s priority is on reforming and empowering agencies like the Broadcasting Board of Governors (BBG) and the newly created Global Engagement Center at the State Department to provide offensive information weapons capable of effectively combating both state and non-state actors who seek to undermine U.S. national security interests and the interests of U.S. allies.
Transatlantic Cooperation Through Information Sharing
The flexibility of the last goal is key, because there is much more to cybersecurity than attacks led by nation-states. This year, most momentum in Congress and the new administration is unifying around the National Doctrine of Deterrence—a concept focused on defeating nation-based cyber threats such as disinformation campaigns and cyber hacks or attacks disabling public sector resources. But the United States and its allies should be investing in and improving on its Cyber Early Warning Systems (CEWS) to ensure cyber threats from new sources—whether nation-state actor, terrorist, or a cybercriminal acting alone—are thwarted before they happen. Such CEWS are only as good as the intelligence and updated data sets flowing into its systems, however. For these to be more efficient, there must be increased cooperation across U.S. agencies and with its allies abroad about the sources and nature of threats.
While the NSA scandal and the Snowden leaks caused rifts between intelligence agencies who once cooperated closely, new common threats from Russia and beyond should wake allies to the benefits of information sharing on cyber threats and establishing common compliance mechanisms.
“Clearly, a greater degree of both bilateral and multilateral cooperation is needed,” said Steve Bucci, a visiting fellow at the Heritage Foundation. “Both countries should seek to establish new exchanges of information and threats, directly with each other, and through NATO. The foolishness that came out after the Snowden revelations should be left to the public, while the two governments move past that.”
While information-sharing channels exist within NATO (Cyber Defense Committee and the Nation Communication and Information Agency) and the European Union (EC3, or Europol’s cybercrime center) cooperation is not expansive or active enough to meet the newest cyber threats, especially those posed to national, and international, security.
“Extensive information sharing must be done with little or no delay or hold backs. Cyber threat information must be widely shared,” Mr. Bucci said, adding that NATO should be the fora for this information sharing, and that Germany and the U.S. could mutually agree to a bilateral information sharing and self-defense agreement which could be pursued for active defense purposes. Here, the United States could support the transfer and training of cyber capabilities to increase protection and long-term development of cyber capabilities in a country such as Germany, so that long term, it will have its own capabilities and can support other allies in the region.[14]
The Vital Role of the Private Sector
Until Germany and the United States are willing to share vital threat information with each other more directly, the private sector is often bridging the gap left on new threat information, and providing solutions to ensure risk management. Global companies such as Microsoft and Google do not see cyber threats in a nation-state paradigm.
“Cybersecurity threats are not limited to territorial boundaries, and as a global company our priority is defense—protecting our customers from the broad range of threats wherever they are,” said Christopher Krebs, Director for Cybersecurity Policy from Microsoft. Yet tech and Internet companies, both large and small, are often keeping ahead of the newest cyber challenges while government agencies are slowed by infighting and bureaucracy that can prevent outside-the-box solutions to new challenges.
“The private sector has far surpassed governments as the ‘font’ of innovation. The economies of the U.S. and Germany are inextricably linked. The incredible power of our private sectors must be brought into the fight,” said Mr. Bucci, who himself used to be a top strategist in IBM’s cybersecurity campaign.
Christopher Painter, the Coordinator for Cyber Issues at the U.S. Department of State, said that in Germany all stakeholders needed to be aware of and active in cybersecurity, including a broad range of companies. Though some sectors have led the way, there is a lot left to do, he said.
Agreement on Cybersecurity Norms
Another challenge to the U.S.-German partnership in enhancing cybersecurity has been a fixation on different starting points in the conversation of what needs to be addressed first. While Germany is focused on privacy regulation, and the protection of data, the United States is discussing how offensive its cyberwarfare may be—for better or worse.
The SASC Cybersecurity Subcommittee will be looking at guidelines for the Pentagon on what actions are allowable against a cybersecurity actor before an attack takes place, and what kinds of responses will be permitted. “Should you limit an attack in cyberspace to a response in cyberspace? I think the answer is no. You have multiple domains in which to respond,” Senator Rounds said this month.[15]
And while the Germans tend to look to international law for the limits on its cyber warfare capacity, the United States would be happy if even voluntary norms set by countries for cyberspace would actually work. What is clear is that a consensus is urgently needed on what is considered an act of warfare in cyberspace, and how to penalize actors who intentionally cause harm, including damage to weapon systems, critical infrastructure, and loss of life as a result of cyber attacks.
Mr. Painter stated that the international cyber stability framework the U.S. government was advancing affirms that international law applies to state behavior in cyberspace, and articulates certain voluntary norms and confidence building measures.[16]
“When there is unacceptable conduct in cyberspace, sustained pressure by the United States and other country partners can be used to ensure compliance,” he said. The United States has a range of tools at its disposal including economic, law enforcement, diplomatic and, in appropriate circumstances, military.
“When there is a breach, sustained pressure by the United States and other country partners should be used to ensure compliance,” he said. No tool—financial, defense, or judicial—should be left off the table.
By cementing what actions may be allowable to protect national security, and which should be punishable, and how, and by whom, democracies such as Germany and the United States can expand their influence, increase their security, and together, isolate non-democratic regimes. Such isolation of cyber enemies—rather than of long-time allies—is a necessary first step to improving cybersecurity in 2017.
[1] The President of the Bundesamt für Verfassungsschutz Hans-Georg Maassen was cited in Stefan Wagstyl, “German politics: Russia’s next target?” Financial Times, 29 January 2017.
[2] Jeremy Diamond, “Russian Hacking and the 2016 Election,” CNN, 16 December 2016.
[3] In their interpretation of the social mechanisms of crisis resilience in the transatlantic context, the Institut für Politische Wissenschaft at Ruprecht-Karls-Universität Heidelberg stated in a paper for the workshop “Crisis, the politics of resilience and the future of transatlantic relations” in 2017 that: “1.) Since democratic countries tend to build stronger institutional ties than other regimes, these institutions will prevent or ameliorate crises through information sharing. 2.) Transatlantic democracies have established a persistent system of division of labor and 3.) The transatlantic community’s strategy of expanding the sphere of democracies, by integration, cooperation or force, has alienated non-democratic regimes, fostering adversarial security outlooks and non-democratic cooperation, which in turn may stabilize security cooperation among democratic nations”. This analytical lense informs my recommendations.
[4] Anja Schmoll-Trautman, “Cyber-Angriffe in Deutschland verursachen Milliarden Euro Schaden,” Silicon.de, 25 May 2016. See also: Sam Schofield, “Protecting America’s Private Sector from Cyber Attacks: Why it’s Vital to National Security,” Foreign Policy, 5 August 2016. In 2014, this meant a loss of 1.6% GDP in Germany, and .64% of GDP in the United States, according to the Ponemon Institute’s 2014 Global Report on the Cost of Cybercrime.
[5] Senate Armed Services Committee, Joint Statement for the Record, “Foreign Cyber Threats to the United States,” The Honorable James R. Clapper, Director of National Intelligence, The Honorable Marcel Lettre, Undersecretary of Defense for Intelligence, Admiral Michael S. Rogers, USN Commander, U.S. Cyber Command, Director, National Security Agency, 5 January 2017.
[6] Verteidigungsministerium, “47 Millionen Hackerangriffe auf die Bundeswehr,“ 12 January 2017.
[7] “Bundeswehr zählte 71 Millionen Cyberattacken 2015,“ Spiegel Online, 16 March 2016.
[8] Isabel Skierka, “Cybersecurity, the German Way,” Observer Research Foundation, 20 October 2016.
[9] Ibid.
[10] Bundesministerium des Inneren, “Cybersicherheitsstrategie für Deutschland 2016,” November 2016, 9.
[11] Of that, $3.1 billion was to go to modernizing technologies across the federal government, and $62 million for cyber professionals. See: Dustin Volz and Mark Hozenball, “Concerned by cyber threat, Obama seeks big increase in funding” Reuters, 10 February 2016. While Congress has not passed the FY2017 budget, the government is being funded by a continuing resolution through April 2017. Proposed amounts for spending set a cap, but how much will actually be spent is decided within Congressional subcommittees. By comparison, the 2017 Defense Appropriations bill requests $58.6 billion for Global War on Terrorism funding.
[12] National Defense Authorization Act, HR 4909, The National Defense Authorization Act for Fiscal Year 2017, https://armedservices.house.gov/sites/republicans.armedservices.house.gov/files/wysiwyg_uploaded/FY17%20NDAA%20Summary.pdf. $8.7 billion was requested for counterterrorism efforts Department of Defense, https://www.defense.gov/Portals/1/features/2016/0216_budget/docs/2-4-16_Consolidated_DoD_FY17_Budget_Fact_Sheet.pdf.
[13] Senator Mike Rounds, Senate Press Release, “Rounds to Chair Newly Formed Subcommittee on Cybersecurity,” 18 January 2017.
[14] Franklin D. Kramer, Robert J. Butler, Catherine Lotrionte, “Cyber and Deterrence: The Military-Civil Nexus in High-End Conflict,” Atlantic Council, January 2017.
[15] Brendan Bordelon, “Rounds is Ready to Lead New Senate Cybersecurity Subcommittee,” Morning Consult, 1 February 2017.
[16] See recommendations on future norms and potential treaty obligations in: “A Framework for International Cyber Stability,” International Security Advisory Board, 2 July 2014, https://www.state.gov/documents/organization/229235.pdf.