New Cyberattacks in Germany: The Elephant Is Already in The Room

Axel Spies
German attorney-at-law (Rechtsanwalt)
Dr. Axel Spies is a German attorney (Rechtsanwalt) in Washington, DC, and co-publisher of the German journals Multi-Media-Recht (MMR) and Zeitschrift für Datenschutz (ZD).
The Romans were shouting “Hannibal at the gates” when the famous general from Carthage tried to conquer their city with elephants in 218 BC. Today’s cyber-warriors and cyber-criminals are already behind the gates, using subtler means to invade the computers of individuals, companies, and even governments. And we may not even know the attackers. Many attacks could immediately affect devices in everyone’s office or otherwise at hand. In the most recent case in Germany, it is not entirely clear what has happened, but at its peak 900,000 DSL routers of a large German telecommunications group came under attack. Many had to be shut down temporarily, which led to serious temporary disruptions and customer concerns. According to the BSI, the German Cyber Security Agency, government networks were also attacked with malware, but the attack was successfully fended off. While software updates and patches prevented worse consequences, a number of shortcomings became apparent:
- The root cause was a concerted worldwide attack with the goal to create a so-called “bot net” to overtake the devices and control them remotely.
- The German company was not specifically targeted. There is no evidence that its customer data were compromised. Insiders reported that the malware was poorly written and didn’t cause the intended damage.
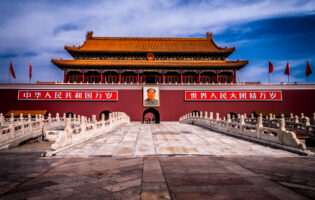
- It remains unclear who masterminded the attack. There has been immediate finger pointing at Russia and China, but there is no clear evidence for this allegation. The perpetrators could be foreign governments, criminals located anywhere who blackmail the targets, or hackers who simply take pleasure in shutting down a vital system.
This is not the first time that Germany came under attack. In 2015, the German Bundestag’s network and the website of the Chancellery were targeted. And it was suspected at this time, without clear proof at hand, that Russia was behind it. After the recent new wave of attacks made a lot of headlines, Chancellor Angela Merkel quickly stepped before the press, indirectly blaming Russia: “Such cyber-attacks, or hybrid confrontations, as they are called in the doctrine of Russia, are now part of everyday life. We must learn to deal with it,” she said.
Politicians and Agencies Jump into Action
But how to deal with it? Merkel has some personal interest in the topic. In view of the disclosures of information during the recent U.S. campaign, there is additional concern that the German elections this year will come under attack and sensitive information will be disclosed or compromised. Merkel stresses correctly that there is no need for panic. There is still a lot of mere speculation floating around regarding who could be behind the recent attack. But obviously this new wave of attacks is a wake-up call for some politicians. Federal interior minister Thomas de Mazière wants to beef up and expand the product liability rules for software and hardware. The idea behind these efforts is that maintenance for software and hardware is poor and sometimes lacking. Any line of defense against such attacks is only as good as its weakest link. Therefore, some German politicians want to get the manufacturers and service providers legally on the hook to provide more network security and hold them responsible. It is thus likely that cybersecurity will become a campaign topic that the opposition (Linke, Greens) will gladly embrace.
The long-term impact of the recent attacks in Germany is much broader. While the issue is not new, the recent events leave many German companies and citizens worried that their data and devices may not be safe if they store data and other sensitive information, for instance, in “the Cloud.” Their dilemma is that most of them gladly embrace the conveniences the new devices bring and face economic and competitive pressure to use Cloud computing and decentralized data and software storage to reduce costs. Not using the equipment or the Cloud services may not be an option in today’s global economy. Given how international networks function and how cyberattacks operate, just storing data in Germany is not sufficient to shield them from cyber-warriors. One way to deal with the issue is through the platforms and the advice that the BSI provides for “critical infrastructure.” Based on the IT Security Act of 2015, the BSI has a lot of work on its plate. The ordinance defining “critical infrastructure” is not even published. The BSI estimates that “450 facilities” will be covered by that definition, which is only the tip of the iceberg. While stepping forward, the BSI should deepen its discussions with the U.S. counterparts and learn from the U.S. counterparts in their implementation of the U.S. Computer Fraud and Abuse Act and the Cybersecurity Act of 2015.
Industry Cooperation Is A Key Component
Whatever the BSI may determine, bottom-up initiatives will be needed to beef up security and a functioning alert system. There is hardly any other choice. Companies must cooperate if there is an attack. A new GWU report for the United States shows that while the U.S. government will always play an important role in cybersecurity, it lacks the resources to fully defend the private sector. A first step would be to lay out the strengths and weaknesses of industry practices and move to apply active defense measures (such as “hacking back”). In addition, business codes and practices such as the recent data protection code of conduct released by the Cloud Infrastructure Services Providers in Europe (CISPE) have been developed and could mitigate the problem. For instance, a core piece of the new CISPE code is a Service Agreement that addresses the division of responsibilities between the Cloud computing provider and the customer for the security of the service. This is a core issue. It also addresses the need for certifications by an independent third party auditor that the service is safe. Such codes are needed to protect industry and consumers against weak links in the network that could be prone to attacks. Many companies and agencies don’t even know that their systems are left unprotected. Educating them and, more generally, the public about this is not an easy feat. The measures must be balanced against important considerations such as the protection of individual liberties, privacy, and the risk of collateral damage. “Hacking back” may not work when the attacker’s device is only a dummy computer. Smarter, more nimble approaches may be needed. Further collaboration between the private sector and policymakers across the borders is probably overdue.
Dr. Axel Spies, Morgan Lewis & Bockius, Washington, DC. Dr. Spies is the author of AGI Issue Brief 46: German/U.S. Data Transfers: Crucial for Both Economies, Difficult to Regain Trust